CSSA 2023: Rethinking the approach to cybersecurity
12 September 2023 | Story Nicole Forrest. Photos Lerato Maduna. Read time 8 min.
The seventh Cyber Security Symposium Africa (CSSA) kicked off at the University of Cape Town (UCT) on Wednesday, 6 September. The event, which was the first in-person conference in the series since 2019, took place at the Wilfred & Jules Kramer Law Building on middle campus.
Organised by UCT’s Information and Communication Technology Services (ICTS) department in collaboration with the Cybersecurity Capacity Centre for Southern Africa (C3SA), the CSSA focused on the imperatives of cyber security in an ever-changing world.
Cybercrime is currently the most widespread form of crime globally and, with cybercriminals constantly adapting their attacks, therefore it’s essential that every individual is equipped with the tools they need to identify potential cybercrimes.
Understanding this, ICTS aimed to help attendees secure business assets by enabling them to rethink their approach to awareness communication, training and cybersecurity architecture.
“The theme of cybersecurity in an ever-changing environment, rethinking the approach to comms and awareness and training, I think, is very timeless,” said the executive director of ICTS, Richard van Huyssteen, in his welcome address.

“All of us either know someone … who has been the victim of some kind of cybercrime, either because it was a collective event in which some asset … or some virtual information was compromised, or you yourself were the victim of a scam.
“What that really demonstrates is something that we really know very well: that information security is not just for the techies. It is all-consuming and all-influencing and affecting part of everybody’s daily digital life.”
Keeping cyberspace clean
Van Huyssteen’s point was echoed by Siya Ndlovu, a senior cybersecurity consultant at insurance brokerage and risk advisory firm Marsh in his address around cyber hygiene. However, he noted that awareness training is an essential tool in this regard.
“As an organisation, you need to have controls in place to make sure that external threats do not penetrate your organisation,” he said.
“So, you will have controls like password controls; you will have your firewall; you update your systems and software regularly to ensure that external threats cannot exploit the vulnerabilities that will be found in outdated software or end-of-life systems.
“But cyber hygiene is also about cultivating a security-centric mindset, or security-centric habits. That involves teaching users what they must do to make sure that they don’t fall victim to identity theft or that they don’t compromise their organisation’s infrastructure.
“We must focus on highlighting the importance to these individuals of not sharing too much PII [personal identifiable information] or passwords, because these are the most common entry points that hackers use when they want to penetrate organisations.”
Opportunities for South Africa
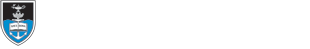
Zooming out to look at the state of cybersecurity in South Africa and the world, Professor Basie von Solms of the University of Johannesburg and a member of the technical board of C3SA, discussed the Cybersecurity Capacity Maturity Model for Nations (CMM) and how this is used to evaluate countries’ cybersecurity status.
According to Professor Von Solms, the CMM allows states to benchmark a detailed, pragmatic set of actions to establish the degree of development of the nation’s cybersecurity actions. This then allows governments, the private sector, civil society and others to come together and identify priorities for future investment and capacity building.
“What are the benefits of this? First, increased cybersecurity awareness and capacity building and greater collaboration within government. One of the greatest benefits is that through this stakeholder group – this collaboration, this understanding – the sharing is happening on government level and on private industry level,” he said.
“Networking and collaboration with and between business and wider society enhances the eternal credibility of the cybersecurity agenda within governments. This drives the understanding that everybody in a country is actually working towards the same goal.
“So, synergistically, we can be much better. This will help us to define roles and responsibilities within governments, which will, in turn, provide evidence for increasing funding for cybersecurity capacity building. And lay the foundation for a country strategy and national development policy.”
Despite this array of benefits, however, Von Solms noted that South Africa has been slow on the uptake when it comes to assessing its cybersecurity status.
“We’ve tried to convince the South African government several times to expose [itself] to such a maturity evaluation so that we can see what’s going on. There are many projects happening in South Africa – very good projects – but they’re not coordinated. We don’t know about them and that is one of the benefits of this maturity evaluation.
“We want to know in terms of cybersecurity awareness programmes, what you are doing and what’s that company doing, and that company? Are we overlapping? Why can’t we share efforts and be synergistic to benefit the country as a whole?”
Africa rising
Staying with the African outlook, group product manager at Liquid Intelligent Technologies South Africa, Unathi Mothiba, considered the state of cybercrime in the era of cloud adoption.
Mothiba noted that the rise of a distributed, hybrid workforce that increasingly uses personal devices for work tasks within organisations that have little to no consistency around the structure and approach to managing project and meeting documentation poses a major threat.
“If you consider digital transformation and the move towards cloud adoption, we start talking about autonomous computing and the like. We need to accept the level of risk that comes with these developments and think about how we can mitigate against that,” he said.
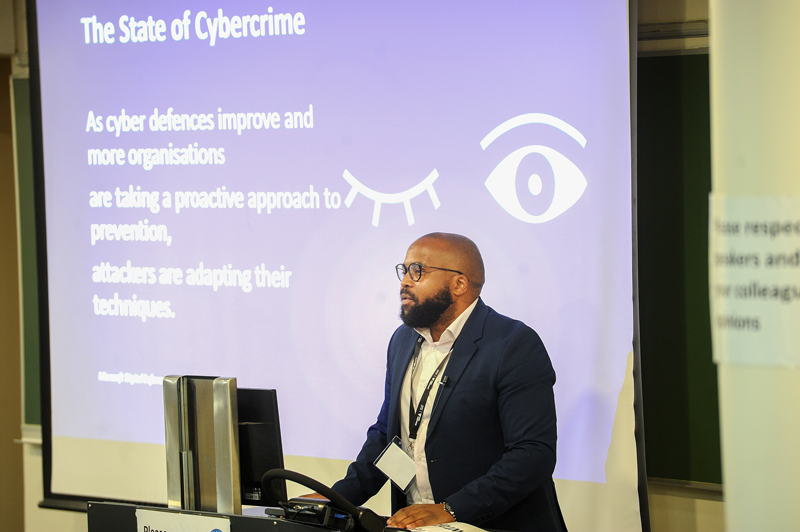
The challenge for Africa, he noted, is not only in developing defences against these attacks, but in ensuring that these solutions are homegrown.
“So, as cyber defences improve and organisations are taking a proactive approach to prevention, attackers are adapting their techniques. This has the ability to assist in moving us as an industry forward, as much as it has an equal negative correlation from a threat actor perspective.
“What is somewhat disappointing is that a lot of our security solutions tend to be imported. I think there’s a lot of capability on the continent. I’ve met with some vendors across the continent, but as it stands, a lot of products and solutions that we could produce are coming from multinational companies.
“For me, that’s a problem because we need to be able to solve our own solutions by creating our own level of firewalls or levels of email security, endpoint protection and the like. Then this becomes a lot more affordable.
“So, I think going forward, what we should be trying to create, or foster, is cultural innovation across the continent and building out the solutions that solve all African-related problems.”
A cyber success
The three-day programme was delivered to more than 1 000 attendees and spanned a variety of topics, including cyber hygiene, cybersecurity and artificial intelligence (AI), threat detection and incident response, as well as digital forensics and blockchain.
However, as Van Huyssteen pointed out, the central focus of the event was to better prepare people for the constantly increasing risks posed by cybercrime.
“Our first line of defence is people, and our most vulnerable attack surface is people. And it will continue to be that way, I’m sure, and social engineering has simply matured in line with the kinds of tools and available assets that exist behind and within our information security systems,” he said.
 This work is licensed under a Creative Commons Attribution-NoDerivatives 4.0 International License.
This work is licensed under a Creative Commons Attribution-NoDerivatives 4.0 International License.
Please view the republishing articles page for more information.